Supermicro Security Centerは、エンタープライズコンピューティング、ストレージ、ネットワーキング、およびグリーンコンピューティング技術におけるグローバルリーダーであるSupermicroからの製品セキュリティアップデートおよび情報の確立された情報源です。当社は、セキュリティプラクティスの継続的な改善に努めています。
お客様のセキュリティは最優先事項であり、Supermicroサーバーおよびストレージシステムの運用を保護するための対策を講じています。今日存在するサーバーおよびストレージシステムは、セキュリティを確保する必要性から、より多機能かつ複雑になっています。脅威アクターに対して、Supermicroはユーザーとお客様を保護するための防御メカニズムを開発し、業界最高水準のセキュリティ知識を提供しています。Supermicroは、お客様が高いセキュリティ基準を満たす製品の導入を期待していることを認識しており、そのため、当社の対応は最高レベルの保護を提供するように設計されています。
Supermicroは、オペレーティングシステムを最新の状態に保ち、ファームウェアとすべてのソフトウェアの最新バージョンを実行することを含む、セキュリティのベストプラクティスに従うことを推奨します。
ライフサイクル・サイバーセキュリティ製品保護
Supermicroは、米国のみで製造された3つのサーバー製品を提供しています。米国の工場に製造を集中させることで、システムの完全性が維持されます。これらの「Made in the USA」製品は、海外からのサイバーセキュリティ侵入の機会を低減し、世界中の顧客に提供されています。このプログラムの詳細については、Made in the USAソリューションページをご覧ください。
Supermicro は、サプライチェーンシステム全体を通じてサイバーセキュリティ対策を厳格に管理しており、調達と生産から運用、そして製品の自然な耐用年数の終了に至るまで、より広範な「揺りかごから墓場まで」のアプローチで製品のセキュリティを確保しています。
Supermicroのベストプラクティスは、豊富なセキュリティ機能によってサポートされる製品セキュリティ要件を満たすように設計されています。これらの機能は、Supermicro製品が業界のセキュリティ標準を満たしていることをお客様に保証します。
最終更新日
Supermicro 、お客様のデータセンターのセキュリティを最優先事項Supermicro Supermicro 。Supermicro 、新たにリリースされた X14/H14 および X13およびH13およびR13 およびX12/H12シリーズのサーバーおよびストレージシステム。これらの組み込み機能は、データセンター内での安全な運用を確立するための指針となります。以下のリストをご確認ください。
| カテゴリー | セキュリティ仕様 | インテル X14 製品 | AMD H14製品 | インテル X13 製品 | AMD H13製品 | Ampere R13製品1 | インテル X12 製品 | AMD H12製品 |
|---|---|---|---|---|---|---|---|---|
| ハードウェア | 信頼のシリコン・ルート | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
| シャーシ侵入保護 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| トラステッド・プラットフォーム・モジュール(TPM)2.0 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| BMCTPM1 | ✔ | ✔ | ✔ | ✔ | ||||
| インテルブートガード | ✔ | ✔ | ✔ | |||||
| インテル® ソフトウェア・ガード・エクステンション(インテル® SGX)1 | ✔ | ✔ | ✔ | |||||
| AMD Secure Processor | ✔ | ✔ | ✔ | |||||
| AMD Secure Memory Encryption (SME) | ✔ | ✔ | ✔ | |||||
| AMD Secure Encrypted Virtualization (SEV) | ✔ | ✔ | ✔ | |||||
| BIOS/BMC | セキュアブート | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
| 安全なドライブ消去 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| セキュアフラッシュ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| セキュアなファームウェア・アップデート | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 暗号署名付きファームウェア | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| セキュアなRedfish API3 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| パスワードのセキュリティ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| USBダイナミックイネーブル/ディセーブル | ✔ | ✔ | ||||||
| HDDパスワード | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| BMC固有パスワード | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| 自動ファームウェアリカバリ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| アンチロールバック | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| ランタイム BMC プロテクション | ✔ | ✔ | ✔ | ✔ | ||||
| システム・ロックダウン | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| サプライチェーンのセキュリティ遠隔認証 | ✔ | ✔ | ✔ | ✔ | ||||
| ドライブキー管理(スーパーガーディアンズ) | ✔ | ✔ | ✔ | ✔ | ✔ | |||
| IPMI 2.0ユーザーロック | ✔ | ✔ | ✔ | ✔ | ✔ | |||
| セキュリティ状態の監視 | ✔ | ✔ | ✔ | ✔ | ||||
| セキュリティ・プロトコルおよびデータ・モデル(SPDM)管理2 | ✔ | ✔ | ✔ | ✔ | ||||
| 規格 | NIST SP 800-193 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| NIST SP 800-147b | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| NIST SP 800-88 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
注意事項
- 一部の機能は、すべての製品に適用されるわけではありません。
- 1一部のモデルおよび構成について
- 22024年第4四半期を予定
- 3TLS v1.2 / v1.3対応。RMCP+ 暗号スイート3 / 17 対応
ベースボード管理コントローラ(BMC)は、ネットワークの異なる場所にいる複数のユーザーにリモートアクセスを提供します。BMCにより、システム管理者はシステムの健全性を監視し、リモートでコンピュータイベントを管理することができます。BMCは、IPMI管理ユーティリティ(Intelligent Platform Management Interface)とともに使用され、サーバーを集中的に制御および監視することができます。BMCは、お客様の要件に対応する幅広いセキュリティ機能を備えています。

データセンターでBMC機能を有効にしたサーバーを管理するためのセキュリティ・ベスト・プラクティス
認証プロセスを活用した動的システム検証
システム認証を使用したハードウェアとファームウェアの変更の検出
暗号署名されたBMCファームウェア
BMC ファームウェアおよび BIOS に暗号署名するセキュリティ機能について説明します。
BMC独自のパスワードセキュリティ機能
BMC Unique Passwordのメリットについてご紹介します。
Intel Platform Update (IPU) アップデート 2026.2、2026年5月
このアップデートは、Intel Xeon® およびその他の Intel プロセッサーを搭載した X14 ファミリーの製品に適用されます。Intel Platform Update (IPU) は、これまで個別に提供されていたセキュリティ・アップデートをまとめて提供します。
- INTEL-SA-01420 – 2026.2 IPU - Intel® プロセッサー・ファームウェアに関するアドバイザリ
AMDセキュリティ情報 AMD-SB-3030、2026年5月
Supermicro 、AMD Secure Process(ASP)およびAMD Secure Encrypted Virtualization – Secure Nested Paging(SEV-SNP)に影響を及ぼす、AMD EPYC™およびAMD EPYC™ Embeddedプロセッサプラットフォームにおける潜在的な脆弱性、ならびにAMD Secure Process(ASP)およびAMD Secure Encrypted Virtualizationに影響を及ぼす、AMD EPYC™およびAMD EPYC™ Embeddedプロセッサプラットフォームにおける潜在的な脆弱性をSupermicro – セキュア・ネステッド・ペイジング(SEV-SNP)に影響を及ぼす可能性のある脆弱性について認識しております。AMDは、この脆弱性に対する緩和策を公開しました。この脆弱性は、Supermicro 、H13、およびH14製品のBIOSに影響を及ぼします。
- CVE-2024-36315
- CVE-2025-61971
- CVE-2025-61972
Intel Platform Update (IPU) アップデート 2026.1 第2部、2026年5月
このアップデートは、Intel Xeon® およびその他の Intel プロセッサーを搭載した X13 シリーズ製品に適用されます。Intel Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートをまとめて提供します。
- INTEL-SA-01413 – 2026.1 IPU - UEFI リファレンスファームウェアに関するアドバイザリ
AMDセキュリティ情報 AMD-SB-7054、2026年4月
Supermicroは、LocateProtocol Serviceの不適切な使用により、Ring 0からSystem Management Mode (SMM)への特権昇格が発生し、任意のコード実行につながる可能性があるというセキュリティ問題を認識しています。AMDはこの脆弱性に対する緩和策をリリースしました。この脆弱性は、Supermicro H12、H13、およびH14製品のBIOSに影響を与えます。
- CVE-2025-54502
AMDセキュリティ情報 AMD-SB-3034、2026年4月
Supermicroは、特権を持つ攻撃者がMemory Mapped I/O (MMIO)ルーティング構成レジスタを改ざんし、SEV-SNPゲストメモリの整合性を損なう可能性があるというセキュリティ問題を認識しています。AMDはこの脆弱性に対する緩和策をリリースしました。この脆弱性は、Supermicro H12、H13、およびH14製品のBIOSに影響を与えます。
- CVE-2025-54510
AMDセキュリティ情報 AMD-SB-3016、2026年4月
Supermicroは、内部セキュリティ監査により、悪意のあるHypervisorがIOMMUを介してSecure Encrypted Virtualization-Secure Nested Paging (SEV-SNP)ゲストメモリに書き込むことを可能にする潜在的な脆弱性が発見されたというセキュリティ問題を認識しています。AMDはこの脆弱性に対する緩和策をリリースしました。この脆弱性は、Supermicro H12、H13、およびH14製品のBIOSに影響を与えます。
- CVE-2023-20585
Intel Platform Update (IPU) アップデート 2025.3 第2部、2026年3月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、X13、X14 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-01234 – 2025.3 IPU - UEFI リファレンス・ファームウェアに関するアドバイザリ
AMDセキュリティ速報 AMD-SB-7059、2026年2月
Supermicroは、ゲスト仮想マシン (VM) がホストシステムをクラッシュさせる可能性のあるセキュリティ問題を認識しています。AMDはこの脆弱性に対する緩和策をリリースしました。この脆弱性は、Supermicro H11、H12、H13、およびH14製品のBIOSに影響を与えます。
- CVE-2023-31364
インテル プラットフォーム アップデート (IPU) アップデート 2026.1、2026年2月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、X13、X14 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-01314 – 2025.4 IPU - インテル® TDX モジュールに関するお知らせ
- INTEL-SA-01315 – 2026.1 IPU - インテル® チップセット ファームウェア アドバイザリ
- INTEL-SA-01396 – 2026.1 IPU - インテル® プロセッサー ファームウェア アドバイザリ
- INTEL-SA-01397 – 2026.1 IPU - Intel® Trust Domain Extensions (Intel® TDX) モジュール アドバイザリ
AMDセキュリティ情報 AMD-SB-3023、2026年2月
Supermicroは、I/Oメモリ管理ユニット (IOMMU)、AMD Secure Encrypted Virtualization – Secure Nested Paging (SEV-SNP)、およびその他のプラットフォームコンポーネントに影響を与える、AMD EPYC™ プロセッサープラットフォームにおける潜在的な脆弱性を認識しており、これらは内部および第三者による監査中に発見されました。この脆弱性は、Supermicro H11、H12、H13、およびH14製品のBIOSに影響を与えます。
- CVE-2025-52533、CVE-2025-29950、CVE-2024-36355、CVE-2025-29939、CVE-2025-0012、CVE-2025-52536、CVE-2024-21961、 CVE-2025-29948、CVE-2024-21953、CVE-2025-29952、CVE-2025-52534、CVE-2025-54514、CVE-2025-48517、 CVE-2025-0031、CVE-2024-36310、CVE-2025-29946、CVE-2025-48514、CVE-2025-0029、CVE-2025-48509
マイクロソフト セキュア ブート認証局 2011 年 サポート終了のお知らせ:2023 年発行証明書への移行について
MicrosoftのSecure Boot CA 2011証明書は2026年6月に期限切れとなり、その後、それらにのみ依存するデバイスは、Windows Boot ManagerおよびSecure Bootコンポーネントのセキュリティ更新プログラムを受け取らなくなり、ブートキットの脆弱性リスクが増大します。Microsoftは新しい2023年証明書への移行を進めており、Supermicroは対応するBIOSアップデートをリリースしています。ユーザーはSecure Bootを有効にし、最新のBIOS/ファームウェアをインストールし、すべてのアップデートを適用する必要があります。ほとんどのシステムでは、サポートされているデバイスで移行が自動的に行われるため、直ちに対応する必要はありません。
詳細を見るSupermicro BMCファームウェアの脆弱性、2026年1月
一部のSupermicroマザーボードで複数のセキュリティ問題が発見されました。これらの問題はSupermicro BMCファームウェアに影響を与えます。
- CVE-2025-12006
- CVE-2025-12007
AMDセキュリティ情報 AMD-SB-3027、2026年1月
Supermicroは、Stale RLB Entryにより、Secure Nested Paging (SNP) のアクティブな仮想中央処理装置 (vCPU) が他の仮想マシン (VM) のTLBエントリを再利用し、データ整合性を損なう可能性のあるセキュリティ問題を認識しています。AMDはこの脆弱性に対する緩和策をリリースしました。この脆弱性は、Supermicro H12およびH14製品のBIOSに影響を与えます。
- CVE-2025-29943
Supermicro BMCファームウェアの脆弱性、2025年11月
一部のSupermicro製ボードおよびCMMにおいて、4つのセキュリティ問題が発見されました。これらの問題は、Supermicro BMCファームウェアに影響を与える可能性があります。
- CVE-2025-7623
- CVE-2025-8076
- CVE-2025-8404
- CVE-2025-8727
AMDセキュリティ情報 AMD-SB-3029、2025年11月
Supermicroは、Stale RLB Entryにより、Secure Nested Paging (SNP) のアクティブな仮想中央処理装置 (vCPU) が他の仮想マシン (VM) のTLBエントリを再利用し、データ整合性を損なう可能性のあるセキュリティ問題を認識しています。AMDはこの脆弱性に対する緩和策をリリースしました。この脆弱性は、Supermicro H12、H13、およびH14製品のBIOSに影響を与えます。
- CVE-2025-29934
Supermicro BMCファームウェアの脆弱性、2025年10月
一部のSupermicroマザーボードおよびCMMで複数のセキュリティ問題が発見されました。これらの問題はSupermicro BMCファームウェアに影響を与えます。
- CVE-2025-7704
AMDセキュリティ情報 AMD-SB-7055、2025年10月
Supermicroは、RDSEED命令がランダム性とは矛盾する頻度で「0」を返し、かつ誤って成功 (CF=1) を通知することで、失敗が成功として誤分類される可能性を示すセキュリティ問題を認識しています。AMDはこの脆弱性に対する緩和策をリリースしました。この脆弱性は、Supermicro H13およびH14製品のBIOSに影響を与えます。
- CVE-2025-62626
AMDセキュリティ速報 AMD-SB-3020、2025年10月
Supermicroは、悪意のあるHypervisorがSecure Nested Paging (SNP) の初期化中にReverse Map Table (RMP) を破損する可能性があるセキュリティ問題を認識しています。この問題は、AMD EPYC™ 第3世代、第4世代、および第5世代プロセッサーに影響します。この脆弱性は、Supermicro H12、H13、およびH14製品のBIOSに影響します。
- CVE-2025-0033
Supermicro BMCファームウェアの脆弱性、2025年9月
一部のSupermicroマザーボードで複数のセキュリティ問題が発見されました。これらの問題はSupermicro BMCファームウェアに影響を与えます。
- CVE-2025-7937
- CVE-2025-6198
インテル・プラットフォーム・アップデート(IPU)2025.2 パート2、2025年8月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、X13、X14 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-01245- 2025.2 IPU - インテル® TDX モジュールに関するアドバイザリー
- INTEL-SA-01249- 2025.2 IPU - インテル® プロセッサー・ストリーム・キャッシュに関するアドバイザリー
インテル・プラットフォーム・アップデート(IPU)2025.3、2025年8月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、X13、X14 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-01280- 2025.3 IPU - インテル® チップセット・ファームウェアに関するアドバイザリー
- INTEL-SA-01312- 2025.3 IPU - インテル® TDX モジュールに関するアドバイザリー
- INTEL-SA-01313- 2025.3 IPU - インテル® Xeon® プロセッサー・ファームウェアに関するアドバイザリー
AMDセキュリティ脆弱性、2025年8月
このアップデートは、第1世代/
- AMD-SB-4012 – AMDクライアントの脆弱性 – 2025年8月
- AMD-SB-3014 – AMDサーバーの脆弱性 – 2025年2月
AMDセキュリティ情報 AMD-SB-7029、2025年7月
Supermicroは、一部のAMDプロセッサーにおける一時的実行セキュリティ脆弱性を認識しています。AMDは、Microsoft®の「Enter, Exit, Page Fault, Leak: Testing Isolation Boundaries for Microarchitectural Leaks」と題されたレポートを調査中に、複数のサイドチャネル攻撃を発見しました。
- CVE-2024-36348
- CVE-2024-36349
- CVE-2024-36350
- CVE-2024-36357
2025.1 IPU - インテル® プロセッサー アドバイザリ、INTEL-TA-01209、2025 年 6 月
Supermicroは、ローカルオペレーティングシステムアクセスを介したユーザー認証を持つ未熟なユーザーが、Intel® CSMEおよびIntel® SPSのIntel® PTTファームウェアにおける境界外読み取りにより、サービス拒否を通じて可用性(高)に影響を与える可能性のあるセキュリティ脆弱性を認識しています。
- CVE-2025-2884
AMDセキュリティ速報 AMD-SB-7039、2025年6月
Supermicroは、権限を持つ攻撃者がx86アーキテクチャからCrypto Co-Processor (CCP) レジスタにアクセスできる可能性があるセキュリティ脆弱性を認識しています。この問題は、AMD EPYC™ 第1世代、第2世代、および第3世代プロセッサー、ならびに一部のH11およびH12世代の製品に影響します。
- CVE-2023-20599
インテル・プラットフォーム・アップデート(IPU)2025.2、2025年5月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、X13、X14 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-01244- 2025.2 IPU - インテル® プロセッサーに関するアドバイザリー
- INTEL-SA-01247- 2025.2 IPU - インテル® プロセッサー間接分岐予測に関するアドバイザリー
2025.1 IPU - インテル® プロセッサー アドバイザリ、INTEL-TA-01153、2025 年 5 月
プロセッサ・イベントまたは予測によって、不正な操作(または不正なデータを含む正しい操作)が一時的に実行され、秘密チャネルを介してデータが公開される可能性があります。間接分岐予測は、強化された IBRS プロパティおよび間接分岐予測バリアによって完全に制約されていない可能性があります。このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、および X13 ファミリーの製品に適用されます。
この脆弱性は、特定のH13 製品のSupermicro BIOS に影響を与えます。Supermicro は、本アドバイザリに記載されているこれらの脆弱性に関する公開発表や悪用を認識していません。
- INTEL-SA-01153 - 2025.1 IPU - インテル® プロセッサーに関するアドバイザリー
AMI セキュリティ勧告 AMI-SA-2025003, 2025年3月
Supermicroは、AMIセキュリティアドバイザリAMI-SA202503で報告された、BIOSファームウェアにおける潜在的な脆弱性を認識しています。Aptio® VのBIOSには、攻撃者がローカル手段によってTime-of-check Time-of-use (TOCTOU) 競合状態を引き起こす可能性のある脆弱性が含まれています。この脆弱性が悪用された場合、任意のコード実行につながる可能性があります。
この脆弱性は、特定のH13 製品のSupermicro BIOS に影響を与えます。Supermicro は、本アドバイザリに記載されているこれらの脆弱性に関する公開発表や悪用を認識していません。
- CVE-2024-54084
AMDセキュリティ・ブリテン AMD-SB-7033、2025年3月
Supermicroは、Google®が報告した「AMDマイクロコード署名検証の脆弱性」として知られるセキュリティ問題について認識しています。これは署名検証アルゴリズムの欠陥によって引き起こされ、この脆弱性により、管理者権限を持つ攻撃者が任意のCPUマイクロコードパッチをロードできる可能性があります。
- CVE-2024-36347
インテル・プラットフォーム・アップデート(IPU)2025.1、2025年2月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、および X13 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-01139- 2025.1 IPU - UEFI ファームウェアに関する勧告
- INTEL-SA-01152- 2025.1 IPU - インテル® チップセット・ファームウェアに関するアドバイザリ
- INTEL-SA-01213- 2025.1 IPU - インテル® SGX アドバイザリ
- INTEL-SA-01228- 2025.1 IPU - 第13世代および第14世代インテル® Core™ プロセッサーに関するアドバイザリー
AMDセキュリティ脆弱性、2025年2月
このアップデートは、第1世代/
- AMD-SB-4008 – AMDクライアント脆弱性 – 2025年2月
- AMD-SB-3009 – AMDサーバー脆弱性 – 2025年2月
AMDセキュリティ速報 AMD-SB-7028、2025年2月
Supermicroは、複数のAMDプロセッサーでサポートされているAmdPlatformRasSspSmm UEFIモジュールにおいて、Eclypsiumによって報告されたSystem Management Mode (SMM) コールアウト脆弱性を認識しています。この問題は、AMD EPYC™ 第2世代プロセッサー、およびH11およびH12世代の製品に影響します。
- CVE-2024-21924
AMDセキュリティ速報 AMD-SB-7027、2025年2月
Supermicroは、複数のAMDプロセッサーでサポートされているAmdPspP2CmboxV2およびAmdCpmDisplayFeatureSMM UEFIモジュール内でQuarkslabによって報告された2つのセキュリティ脆弱性を認識しています。これにより、攻撃者がSMM (System Management Mode) 内でコードを実行できる可能性があります。この問題は、AMD EPYC™ 第1世代、第2世代、第3世代、および第4世代プロセッサー、ならびにH11、H12、およびH13世代の製品に影響します。
- CVE-2024-0179
- CVE-2024-21925
AMDセキュリティ速報 AMD-SB-6016、2025年2月
Supermicroは、Power Management Firmware (PMFW)、AMD System Management Unit (SMU) におけるセキュリティ脆弱性を認識しています。この問題は、AMD H13 MI300X H13DSG-OM製品に影響します。
- CVE-2024-21927
- CVE-2024-21935
- CVE-2024-21936
AMDセキュリティ速報 AMD-SB-6008、2025年2月
Supermicroは、Power Management Firmware (PMFW)、AMD System Management Unit (SMU) におけるセキュリティ脆弱性を認識しています。この問題は、AMD H13 MI300X H13DSG-OM製品に影響します。
- CVE-2024-21971
- CVE-2023-20508
AMDセキュリティ速報 AMD-SB-3019、2025年2月
Supermicroは、Google®が報告したセキュリティ脆弱性を認識しています。この脆弱性では、管理者特権を持つ攻撃者が署名検証アルゴリズムの弱点を悪用し、任意のCPUマイクロコードパッチをロードすることで、機密ゲストのSEVベースの保護が失われる可能性があります。
- CVE-2024-56161
Supermicro BMC IPMIファームウェアの脆弱性、2025年1月
一部のSupermicroマザーボードで複数のセキュリティ問題が発見されました。これらの問題はSupermicro BMCファームウェアに影響を与えます。
- CVE-2024-10237
- CVE-2024-10238
- CVE-2024-10239
AMDセキュリティ速報 AMD-SB-3015、2024年12月
Supermicroは、シリアルプレゼンス検出 (SPD) メタデータを変更して、接続されたメモリモジュールが実際よりも大きく見えるようにすることが可能であり、これによりメモリアドレスエイリアシングが発生する可能性があるセキュリティ問題を認識しています。この問題は、AMD EPYC™ 第3世代および第4世代プロセッサーのマザーボードに影響します。この脆弱性は、Supermicro H12およびH13製品のBIOSに影響します。
- CVE-2024-21944
Supermicro BMC IPMIファームウェアの脆弱性、「Terrapin」、2024年10月
一部のSupermicroマザーボードにおいてセキュリティ上の問題が発見されました。Terrapinの脆弱性により、攻撃者は安全な署名アルゴリズムをダウングレードし、特定のセキュリティ対策を無効にすることができます。Terrapin攻撃には、アクティブな中間者攻撃者が必要です。
- CVE-2023-48795
BIOSの脆弱性、2024年9月
Supermicroは、BIOSファームウェアにおける2つの潜在的な脆弱性を認識しています。これらの脆弱性により、攻撃者がSMRAMに書き込み、RIP/EIPをハイジャックする可能性があります。これらはDenvertonプラットフォームのSupermicro BIOSに影響を与えます。Supermicroは、本アドバイザリに記載されているこれらの脆弱性に関する公表された情報や悪用事例を認識していません。
- CVE-2020-8738
- CVE-2024-44075
インテル・プラットフォーム・アップデート(IPU)2024.3、2024年8月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、および X13 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-01038- 2024.2 IPU - インテル® Core™Ultra プロセッサー・ストリーム・キャッシュに関するアドバイザリー
- INTEL-SA-01046- 2024.2 IPU - インテル® プロセッサー・ストリーム・キャッシュに関するアドバイザリー
- INTEL-SA-00999- 2024.3 IPU - インテル® チップセット・ファームウェアに関するアドバイザリー
- INTEL-SA-01083- 2024.3 IPU - SMI 転送モニタに関するアドバイザリ
- INTEL-SA-01100- 2024.3 IPU - インテル® Xeon® プロセッサーに関するアドバイザリー
- INTEL-SA-01118- 2024.3 IPU - 第3世代インテル® Xeon® スケーラブル・プロセッサー アドバイザリー
- INTEL-SA-01103- 2024.3 IPU - インテル® プロセッサー RAPL インターフェースに関するアドバイザリー
AMDセキュリティ脆弱性、2024年8月
このアップデートは、第1世代/第2世代/第3世代/第4世代 AMD EPYC™ プロセッサーを搭載したH11、H12およびH13製品ファミリーに適用されます。また、Ryzen™ Threadripper™ プロセッサーを搭載したM11/M12およびH13製品ファミリーにも適用されます。様々なプラットフォームコンポーネントにおける潜在的な脆弱性が発見され、AMD EPYC™ および AMD Ryzen™ AGESA™ PI パッケージで軽減されました。
- AMD-SB-4004 – AMDクライアント脆弱性 – 2024年8月
- AMD-SB-3003 – AMDサーバー脆弱性 – 2024年8月
AMDセキュリティ速報 AMD-SB-7014、2024年8月
Supermicroは、SMMロックが有効になっている場合でも、ルートアクセスを持つ攻撃者がSystem Management Mode (SMM) の構成を変更できる可能性があるセキュリティ脆弱性を認識しています。この問題は、AMD EPYC™ 第1世代、第2世代、第3世代、および第4世代プロセッサー、ならびにH11、H12、およびH13世代の製品に影響します。
- CVE-2023-31315
AMDセキュリティ速報 AMD-SB-3011、2024年8月
Supermicroは、悪意のあるハイパーバイザーが、廃止されたSecure Encrypted Virtualization–Secure Nested Paging (SEV-SNP) ゲストVMのメモリを復号できる可能性があるセキュリティ問題を認識しています。この問題は、AMD EPYC™ 第3世代および第4世代プロセッサーのマザーボードに影響します。この脆弱性は、Supermicro H12およびH13製品のBIOSに影響します。
- CVE-2023-31355
- CVE-2024-21978
- CVE-2024-21980
PKFAIL: Supermicro BIOS ファームウェアの脆弱性、2024年7月
Supermicroは、「PKFAIL」として知られるセキュリティ脆弱性の問題を修正しました。この新しい脆弱性により、悪意のあるアクターがオペレーティングシステムから高度なファームウェアレベルの脅威を起動する可能性があります。一部のSupermicro製品が、BIOSの信頼の基点 (Root of Trust) を表す安全でないプラットフォームキー (PK) を使用していることが判明しました。これらの安全でないキーはAmerican Megatrends International (AMI) によって生成され、Supermicroに参照例として提供されました。
詳細を見るOpenSSH "regreSSHion" 脆弱性、2024年7月
特定のSupermicro製マザーボードのBMCファームウェアにおいて、「regreSSHion」として知られるOpenSSHにおけるクリティカルなシグナルハンドラーの競合状態に関するセキュリティ脆弱性が発見されました。この脆弱性により、root権限での認証なしリモートコード実行 (RCE) が発生する可能性があります。
- CVE-2024-6387
BIOSの脆弱性、2024年7月
Supermicroは、BIOSファームウェアにおける潜在的な脆弱性を認識しています。これらの脆弱性は、一部のX11マザーボードに影響を与えます。Supermicroは、本アドバイザリに記載されているこれらの脆弱性に関する公表された情報や悪用事例を認識していません。
- CVE-2024-36432
- CVE-2024-36433
- CVE-2024-36434
Supermicro BMC IPMIファームウェアの脆弱性、2024年7月
一部のSupermicroマザーボードにおいてセキュリティ上の問題が発見されました。この問題は、BMCのウェブサーバーコンポーネントに影響を与えます。Supermicro BMCにおけるこの潜在的な脆弱性は、ファームウェアの「GetValue」関数における入力値のチェック不足によって引き起こされるバッファオーバーフローに起因する可能性があります。
- CVE-2024-36435
AMDセキュリティ情報 AMD-SB-1041、2024年6月
Supermicroは、AMD SPI保護機能における潜在的な脆弱性を認識しています。この問題は、AMD EPYC™ 第1世代、第2世代、および第3世代プロセッサーのマザーボードに影響します。この脆弱性は、Supermicro H11およびH12製品のBIOSに影響します。
- CVE-2022-23829
AMDセキュリティ情報 AMD-SB-4007、2024年5月
Supermicroは、サーバーおよびクライアントのデスクトップおよびモバイルAPU/CPUにおけるAMD DXE (Drive Execution Environment) ドライバーのメモリリークの脆弱性により、高い権限を持つユーザーが機密情報を取得する可能性があることを認識しています。この問題は、AMD EPYC™ 第3世代プロセッサー搭載マザーボードに影響します。この脆弱性はSupermicro H12製品のBIOSに影響します。
- CVE-2023-20594
- CVE-2023-20597
インテル・プラットフォーム・アップデート(IPU)2024.2、2024年5月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X13 ファミリーに適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-01036- 2024.2 IPU - インテル® TDX モジュール・ソフトウェアに関するアドバイザリー
- INTEL-SA-01051- 2024.2 IPU - インテル® プロセッサーに関するアドバイザリー
- INTEL-SA-01052- 2024.2 IPU - インテル® Core™Ultra プロセッサーに関するアドバイザリー
Supermicro BMCファームウェアの脆弱性、2024年4月
一部のSupermicroボードで複数のセキュリティ脆弱性が発見されました。これらの問題(クロスサイトスクリプティングおよびコマンドインジェクション)は、Supermicro BMC IPMI(Web UI)のウェブサーバーコンポーネントに影響を与える可能性があります。これらの潜在的な脆弱性を軽減するために、更新されたBMCファームウェアが作成されました。
- SMC-2024010010(CVE:CVE-2024-36430)
- SMC-2024010011(CVE:CVE-2024-36431)
- SMC-2024010012(CVE:CVE-2023-33413)
インテル® プラットフォーム・アップデート (IPU) 2024.1 および INTEL-TA-00986、2024 年 3 月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、および X13 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00898- 2024.1 IPU - インテル® Atom® プロセッサーに関するアドバイザリー
- INTEL-SA-00923- 2024.1 IPU - インテル® チップセット・ソフトウェアおよび SPS アドバイザリ
- INTEL-SA-00929- 2024.1 IPU - BIOS アドバイザリ
- INTEL-SA-00950- 2024.1 IPU OOB - インテル® プロセッサーに関するアドバイザリー
- INTEL-SA-00960- 2024.1 IPU - インテル® Xeon® プロセッサーに関するアドバイザリー
- INTEL-SA-00972- 2024.1 IPU - インテル® プロセッサー・バス・ロックに関するアドバイザリー
- INTEL-SA-00982- 2024.1 IPU - インテル® プロセッサー・リターン予測アドバイザリー
- INTEL-SA-00986- 第4世代インテル® Xeon® プロセッサーに関するアドバイザリー
- INTEL-SA-01045- 2024.1 IPU OOB - インテル® Xeon® D プロセッサーに関するアドバイザリー
AMDセキュリティ速報 AMD-SB-7009、2024年2月
SupermicroはAMDプロセッサーの脆弱性を認識しています。この問題は、AMD EPYC™ 第1世代、AMD EPYC™ 第2世代、AMD EPYC™ 第3世代、および第4世代プロセッサーに影響します。この脆弱性は、Supermicroの一部のH11、H12、および一部のH13マザーボードに影響します。
- CVE-2023-20576
- CVE-2023-20577
- CVE-2023-20579
- CVE-2023-20587
AMDセキュリティ速報 AMD-SB-3007、2024年2月
SupermicroはSEV-SNPファームウェアの脆弱性を認識しています。この問題は、AMD EPYC™ 第3世代および第4世代プロセッサーに影響します。この脆弱性は、Supermicroの一部のH12および一部のH13マザーボードに影響します。
- CVE-2023-31346
- CVE-2023-31347
PixieFAILの脆弱性、2024年1月
Supermicroは、BIOSファームウェアにおける「PixieFAIL」として知られる潜在的な脆弱性を認識しています。UEFIのオープンソース実装であるTianocore EDKIIのTCP/IPスタック (NetworkPkg) において、複数の脆弱性が発見されました。これらの9つの脆弱性は、ネットワークを介して悪用された場合、リモートコード実行、DoS攻撃、DNSキャッシュポイズニング、および/または機密情報の漏洩につながる可能性があります。PixieFAILは、一部のX11、X12、H11、H12、H13、R12製品のSupermicro BIOSに影響を与えます。Supermicroは、本アドバイザリに記載されているこれらの脆弱性に関する公表された情報や悪用事例を認識していません。
- CVE-2023-45229
- CVE-2023-45230
- CVE-2023-45231
- CVE-2023-45232
- CVE-2023-45233
- CVE-2023-45234
- CVE-2023-45235
- CVE-2023-45236
- CVE-2023-45237
ロゴFAILの脆弱性、2023年12月
Supermicroは、BIOSファームウェアにおける「LogoFAIL」として知られる潜在的な脆弱性を認識しています。BIOSで使用される画像パーサーライブラリにおける不適切な入力検証により、特権を持つユーザーがローカルアクセスを介して権限昇格を可能にする可能性があります。LogoFAILは、一部のX11、X12、X13、H11、M12、R12製品のSupermicro BIOSに影響を与えます。Supermicroは、本アドバイザリに記載されているこれらの脆弱性に関する公表された情報や悪用事例を認識していません。
- CVE-2023-39538
- CVE-2023-39539
Supermicro BMC IPMIファームウェアの脆弱性、2023年12月
- CVE-2023-33411: IPMI BMC SSDP/UPnP ウェブサーバディレクトリトラバーサルおよび iKVM アクセスによる BIOS 再起動許可
- CVE-2023-33412: IPMI BMC 管理用ウェブインターフェイスの仮想フロッピー/USB リモートコマンド実行
- CVE-2023-33413: IPMI BMC デバイスはハードコードされた設定ファイル暗号化キーを使用しており、攻撃者は悪意のある設定ファイルパッケージを作成してアップロードし、リモートでコマンドを実行することができます。
AMDセキュリティ速報 AMD-SB-3005
SupermicroはAMD INVD命令のセキュリティ脆弱性を認識しています。この問題は、第1世代 AMD EPYC™ プロセッサー (SEVおよびSEV-ES)、第2世代 AMD EPYC™ プロセッサー (SEVおよびSEV-ES)、および第3世代 AMD EPYC™ プロセッサー (SEV、SEV-ES、SEV-SNP) に影響します。この脆弱性は、Supermicro H11およびH12マザーボードに影響します。
- CVE-2023-20592
インテル® プラットフォーム・アップデート (IPU) 2023.4 および INTEL-SA-00950 (2023年11月)
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、および X13 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00924- 2023.4 IPU - BIOS アドバイザリ
- INTEL-SA-00950- インテル® プロセッサーに関するアドバイザリー
AMDセキュリティ脆弱性、2023年11月
このアップデートは、第1世代/
- AMD-SN-4002 - AMDクライアント脆弱性 – 2023年11月
- AMD-SN-3002 - AMDサーバー脆弱性 – 2023年11月
Supermicro BMC IPMIファームウェアの脆弱性
一部のSupermicroボードで複数のセキュリティ脆弱性が発見されました。これらの問題(クロスサイトスクリプティングおよびコマンドインジェクション)は、Supermicro BMC IPMI(Web UI)のウェブサーバーコンポーネントに影響を与える可能性があります。これらの潜在的な脆弱性を軽減するために、更新されたBMCファームウェアが作成されました。
- CVE-2023-40289
- CVE-2023-40284
- CVE-2023-40287
- CVE-2023-40288
- CVE-2023-40290
- CVE-2023-40285
- CVE-2023-40286
スタックオーバーフローによる変数の変更
SupermicroのBIOSファームウェアに潜在的な脆弱性が発見されました。攻撃者は、変数を操作して制御フローを乗っ取ることで、Supermicro製マザーボードのこの脆弱性を悪用する可能性があり、カーネルレベルの権限を持つ攻撃者が自身の権限を昇格させ、任意のコードを実行する可能性を許します。
- CVE-2023-34853
AMDセキュリティ速報 AMD-SB-7005
Supermicroは、「INCEPTION」としても知られるリターンアドレス予測器の問題を認識しています。この問題は、AMD EPYC™ 第3世代および第4世代プロセッサーに影響します。この脆弱性は、Supermicroの一部のH12および一部のH13マザーボードに影響します。
- CVE-2023-20569
インテル・プラットフォーム・アップデート(IPU)2023.3、2023年8月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、および X13 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00783- 2023.2 IPU - インテル® チップセット・ファームウェアに関するアドバイザリー
- INTEL-SA-00813- 2023.2 IPU - BIOS アドバイザリ
- INTEL-SA-00828- 2023.2 IPU - インテル® プロセッサーに関するアドバイザリー
- INTEL-SA-00836- 2023.2 IPU - インテル® Xeon® スケーラブル・プロセッサーに関するアドバイザリー
- INTEL-SA-00837- 2023.2 IPU - インテル® Xeon® プロセッサーに関するアドバイザリー
AMDセキュリティ速報 AMD-SB-7008
Supermicroは、「Zenbleed」としても知られるクロスプロセス情報漏洩を認識しています。この問題は、AMD “Zen 2” プロセッサーとしても知られるAMD EPYC™ 7002プロセッサーに影響します。この脆弱性は、Supermicro H11およびH12マザーボードに影響します。
- CVE-2023-20593
SMTP通知におけるシェルインジェクション
一部のSupermicro製ボードにおける脆弱性は、SMTP通知設定に影響を与える可能性があります。この脆弱性により、認証されていない悪意のあるアクターが、アラート設定の件名などのユーザー入力を制御することが可能になり、任意のコード実行につながる可能性があります。
- CVE-2023-35861
サービス・ロケーション・プロトコルSLPにおける反射型サービス拒否(DoS)増幅脆弱性
Service Location Protocol (SLP) は、認証されていないリモートの攻撃者が任意のサービスを登録することを可能にします。これにより、攻撃者はなりすましの UDP トラフィックを使用して、大幅な増幅率でサービス拒否 (DoS) 攻撃を行うことができます。
- CVE-2023-29552
メディア情報Intel BootGuard OEM 秘密鍵が漏洩した可能性、2023 年 5 月
Supermicroがプライベートキーを生成および使用する方法の分析に基づくと、Supermicro製品は影響を受けません。
インテル・プラットフォーム・アップデート(IPU)2023.2、2023年5月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、および X13 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00807- 2023.2 IPU - BIOS アドバイザリ
AMDセキュリティ脆弱性、2023年5月
このアップデートは、第1世代/第2世代/第3世代/第4世代 AMD EPYC™ プロセッサーを搭載したH11、H12、およびH13製品ファミリーに適用されます。このアップデートは、Ryzen™ Threadripper™ プロセッサーを搭載したM12製品ファミリーにも適用されます。さまざまなプラットフォームコンポーネントにおける潜在的な脆弱性が発見され、AMD EPYC™ およびAMD Ryzen™ AGESA™ PIパッケージで軽減されました。
- AMD-SN-4001 - AMDクライアント脆弱性 – 2023年5月
- AMD-SN-3001 - AMDサーバー脆弱性 – 2023年5月
スーパードクター5 アドバイザリー、2023年3月
研究者たちは、Supermicro SuperDoctor5 (SD5) に脆弱性を特定しました。これにより、ウェブインターフェース上の認証済みユーザーであれば誰でも、SuperDoctor5 (SD5) がインストールされているシステム上で任意のコマンドをリモートで実行できる可能性があります。
- CVE-2023-26795
インテル・プラットフォーム・アップデート(IPU)2023.1、2023年2月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11、X12、および X13 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00700- 2023.1 IPU - インテル® Atom® およびインテル® Xeon® スケーラブル・プロセッサー アドバイザリ
- INTEL-SA-00717- 2023.1 IPU - BIOS アドバイザリ
- INTEL-SA-00718- 2023.1 IPU - インテル® チップセット・ファームウェアに関するアドバイザリー
- INTEL-SA-00730- 2023.1 IPU - 第3世代インテル® Xeon® スケーラブル・プロセッサー アドバイザリー
- INTEL-SA-00738- 2023.1 IPU - インテル® Xeon® プロセッサーに関するアドバイザリー
- INTEL-SA-00767- 2023.1 IPU - インテル® プロセッサーに関するアドバイザリー
電圧レギュレータ・モジュール(VRM)と集積回路間(I²C)の過電圧/低電圧化、2023年1月
研究者は、ボード・マネージメント・コントローラー(BMC)の脆弱性を特定しました。この脆弱性は、CPUの指定された動作範囲外で電圧を変更することを可能にし、その結果、正常な計算に影響を及ぼす可能性があります。
- CVE-2022-43309
AMDセキュリティ脆弱性、2023年1月
このアップデートは、第1世代/第2世代/第3世代/第4世代 AMD EPYC™ プロセッサーを搭載したH11およびH12製品ファミリーに適用されます。このアップデートは、Ryzen™ Threadripper™ プロセッサーを搭載したM12製品ファミリーにも適用されます。さまざまなプラットフォームコンポーネントにおける潜在的な脆弱性が発見され、AMD EPYC™ およびAMD Ryzen™ AGESA™ PIパッケージで軽減されました。
- AMD-SN-1031 - AMDクライアント脆弱性 – 2023年1月
- AMD-SN-1032 - AMDサーバー脆弱性 – 2023年1月
インテル・プラットフォーム・アップデート(IPU)2022.3、2022年11月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11 および X12 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00610- 2022.3 IPU - インテル® チップセット・ファームウェアに関するアドバイザリー
- INTEL-SA-00668- 2022.2 IPU - BIOS アドバイザリ
OpenSSLアドバイザリー、2022年11月
OpenSSLバージョン3.xから3.0.6までにおいて、クラッシュや予期せぬ動作につながる可能性のある重大なセキュリティ脆弱性が発見されました。Supermicro製品は、このOpenSSL脆弱性の影響を受けません。
- CVE-2022-3786
- CVE-2022-3602
2022年8月、Microsoft Windowsのセキュアブートバイパス
研究者は、x64 UEFIセキュアブートを使用しているすべてのコンピュータシステムに影響を与える可能性のある、マイクロソフト社のサードパーティ製ブートローダーの複数の脆弱性を特定しました。
- CVE-2022-34301
- CVE-2022-34302
- CVE-2022-34303
インテル・プラットフォーム・アップデート(IPU)2022.2、2022年8月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X11 および X12 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00657- 2022.2 IPU - インテル® プロセッサーに関するアドバイザリー
- INTEL-SA-00669- 2022.2 IPU - インテル® チップセット・ファームウェアに関するアドバイザリー
- INTEL-SA-00686- 2022.2 IPU - BIOS アドバイザリ
インテル・プラットフォーム・アップデート(IPU Update)2022.1、2022年6月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X10、X11、および X12 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00601- 2022.1 IPU - BIOS アドバイザリ
- INTEL-SA-00613- 2022.1 IPU - インテル® Boot Guard およびインテル® TXT アドバイザリー
- INTEL-SA-00614- 2022.1 IPU - インテル® SGX アドバイザリ
- INTEL-SA-00615- 2022.1 IPU - インテル® プロセッサー MMIO Stale Data アドバイザリ
- INTEL-SA-00616- 2022.1 IPU - インテル®Xeon アドバイザリ
- INTEL-SA-00617- 2022.1 IPU - インテル® プロセッサーに関するアドバイザリー
AMDセキュリティ脆弱性、2022年5月
このアップデートは、第1世代/第2世代/第3世代 AMD EPYC™ プロセッサーを搭載したH11およびH12製品ファミリーに適用されます。このアップデートは、Ryzen™ Threadripper™ プロセッサーを搭載したM12製品ファミリーにも適用されます。さまざまなプラットフォームコンポーネントにおける潜在的な脆弱性が発見され、AMD EPYC™ およびAMD Ryzen™ AGESA™ PIパッケージで軽減されました。
- AMD-SN-1027 - AMDクライアント脆弱性 – 2022年5月
- AMD-SN-1028 - AMDサーバーの脆弱性 – 2022年5月
インテル・プラットフォーム・アップデート(IPU)2021.2、2022年2月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X10、X11、および X12 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00470- 2021.2 IPU - インテル® チップセット・ファームウェアに関するアドバイザリー
- INTEL-SA-00527- 2021.2 IPU - BIOS アドバイザリ
- INTEL-SA-00532- 2021.2 IPU - インテル® プロセッサーのブレークポイント制御フローに関するアドバイザリー
- INTEL-SA-00561- 2021.2 IPU - インテル® プロセッサーに関するアドバイザリー
- INTEL-SA-00589- 2021.2 IPU - インテル® Atom® プロセッサーに関するアドバイザリー
SupermicroのApache Log4j脆弱性への対応
Supermicroは、高優先度のCVE-2021-44228 (Apache Log4j 2) 問題(「Log4Shell」とも呼ばれる)、CVE-2021-45046 (Apache Log4j 2) 問題、およびCVE-2021-45105 (Apache Log4j 2) 問題によって引き起こされるリスクを軽減するため、業界と協力して対応しています。Supermicroはまた、Apache Log4j 1.2におけるCVE-2021-4104およびCVE-2019-17571の問題についても認識しています。
ほとんどのSupermicroアプリケーションは、これら5つの脆弱性の影響を受けません。影響を受ける唯一のアプリケーションはSupermicro Power Manager (SPM) です。この問題は、Supermicro Power Manager (SPM) の新バージョンで対処され、リリースは可及的速やかに行われる予定です。SPMにはLog4jバージョン2.17.0が付属します。
Log4j 2
- CVE-2021-44228
- CVE-2021-45046
- CVE-2021-45105
Log4j 1.2
- CVE-2019-17571
- CVE-2021-4104
インテル・プラットフォーム・アップデート(IPU)2021.2、2021年11月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X10、X11、および X12 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00528- 2021.2 IPU - インテル® Atom® プロセッサーに関するアドバイザリー
- INTEL-SA-00562- 2021.1 IPU - BIOS 参照コードに関するアドバイザリ
AMDセキュリティ脆弱性、2021年11月
このアップデートは、第1世代/第2世代/第3世代 AMD EPYC™ プロセッサーを搭載したH11およびH12製品ファミリーに適用されます。様々なプラットフォームコンポーネントにおける潜在的な脆弱性が発見され、AMD EPYC™ AGESA™ PIパッケージで緩和されています。
- AMD-SN-1021 - AMDサーバーの脆弱性 – 2021年11月
インテル セキュリティ アドバイザリ Intel-SA-00525(2021 年 7 月
- INTEL-SA-00525- インテル BSSA (BIOS 共有 SW アーキテクチャ) DFT アドバイザリ
Intel-SA-00525 セキュリティアドバイザリは Supermicro BIOS に影響しません。
詳細を見るインテル・プラットフォーム・アップデート(IPU)2021.1、2021年6月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X10、X11、および X12 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00442- 2021.1 IPU - Intel VT-d アドバイザリ
- INTEL-SA-00459- 2021.1 IPU - Intel-CSME-SPS-TXE-DAL-AMT-Advisory
- INTEL-SA-00463- 2021.1 IPU - BIOS アドバイザリ
- INTEL-SA-00464- 2021.1 IPU - インテル プロセッサーに関するアドバイザリー
- INTEL-SA-00465- 2021.1 IPU - インテル プロセッサー アドバイザリ
SupermicroのTrickboot脆弱性への対応、2021年3月
Supermicroは、X10 UPマザーボードのサブセットでのみ確認されているTrickbootの問題を認識しています。Supermicroは、この脆弱性に対する軽減策を提供します。
TrickBootは、TrickBotマルウェアツールセットの新機能で、脆弱性を発見し、攻撃者がデバイスのBIOSを読み書き/消去できるようにします。
続きを読むBIOSがLinux OSのGRUB2ブートローダーの脆弱性を検出、2020年11月
バージョン 2.06 より前の GRUB2 に欠陥が見つかりました。攻撃者は GRUB2 の欠陥を利用して GRUB 検証プロセスを乗っ取り、改ざんする可能性があります。BIOS はこの状態を検出し、エラーメッセージとともにブートを停止します。
- CVE-2020-10713
インテル・プラットフォーム・アップデート(IPU)2020.2、2020年11月
このアップデートは、インテル® Xeon® およびその他のインテル® プロセッサーを搭載した X10、X11、および X12 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- INTEL-SA-00358- 2020.2 IPU - BIOS アドバイザリ
- INTEL-SA-00391- 2020.2 IPU - インテル® CSME、SPS、TXE、および AMT アドバイザリ
- INTEL-SA-00389- 2020.2 IPU - インテル® RAPL アドバイザリ
- INTEL-SA-00390- インテル BIOS プラットフォームサンプルコードアドバイザリー
インテル月例セキュリティ・アップデート(2020年9月
このアップデートは、インテル® Core® プロセッサーを搭載した X11 および X12 ファミリーの製品に適用されます。インテル® 9 月セキュリティー・アップデートは、これまで個別に提供されていたセキュリティー・アップデートを統合したものです。
なお、X10シリーズにつきましては、今回の発表による影響はございません。
- インテル-SA-00404- インテル® AMT およびインテル® ISM アドバイザリー
インテル・プラットフォーム・アップデート(IPU)2020.1、2020年6月
このアップデートは、インテル® Xeon® プロセッサーを搭載した X10 および X11 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- インテル® CSME、SPS、TXE、AMT および DAL に関するアドバイザリー
- Intel-SA-00320- スペシャルレジスタバッファのデータサンプリングに関するアドバイザリー
- Intel-SA-00322- 2020.1 IPU BIOS アドバイザリ
- インテル-SA-00329- インテル® プロセッサーのデータ漏洩に関するアドバイザリー
- インテル-SA-00260- (更新) インテル® プロセッサー・グラフィックス 2019.2 QSR アップデートに関するアドバイザリー
ErP(エコデザイン)適合のロット9
ロット9規制は、エンタープライズレベルのサーバーなどのデータストレージデバイスに関する新たな製品規格です。Supermicroがロット9コンプライアンスの一環として、サーバーおよびストレージ製品に対する欧州連合(EU)のエコデザイン要件をどのように満たしているかをご確認ください。
詳細を見るインテル2020年2月月例セキュリティ・アップデート
このアップデートは、インテル® Core® プロセッサーを搭載した X11 ファミリーの製品に適用されます。月例インテル® 2 月セキュリティー・アップデートは、これまで個別に提供されていたセキュリティー・アップデートを統合したものです。
- Intel-SA-00307- 権限昇格、サービス拒否、情報開示
インテル月例セキュリティ・アップデート(2019年12月
このアップデートは、インテル® Xeon® プロセッサーを搭載した X10 および X11 ファミリーの製品に適用されます。インテル 12 月セキュリティー・アップデートは、これまで個別に提供されていたセキュリティー・アップデートを統合したものです。
- インテル-SA-00289- インテル® プロセッサー電圧設定の変更に関するアドバイザリー
- Intel-SA-00317- 仮想化環境における予期しないページフォルトに関するアドバイザリー
インテル・プラットフォーム・アップデート(IPU Update)2019.2、2019年11月
このアップデートは、インテル® Xeon® プロセッサーを搭載した X10 および X11 ファミリーの製品に適用されます。インテル® Platform Update (IPU) は、これまで個別に提供されていたセキュリティアップデートを統合したものです。
- Intel-SA-00164- インテル® トラステッド・エグゼキューション・テクノロジー 2019.2 IPU アドバイザリー
- インテル-SA-00219- インテル® SGX 2019.2 インテル® プロセッサー・グラフィックス IPU アップデートに関するアドバイザリー
- インテル-SA-00220- インテル® SGX およびインテル® TXT アドバイザリー
- Intel-SA-00240- Intel CPU Local Privilege Escalation Advisory
- インテル® CSME、サーバー・プラットフォーム・サービス、トラステッド・エグゼキューション・エンジン、インテル® アクティブ・マネジメント・テクノロジーおよびダイナミック・アプリケーション・ローダー 2019.2 IPU アドバイザリー
- インテル-SA-00254- インテル® システム管理モード 2019.2 IPU アドバイザリー
- インテル-SA-00260- インテル® プロセッサー・グラフィックス 2019.2 IPU アドバイザリー
- Intel-SA-00270- TSX トランザクションの非同期中止に関するアドバイザリー
- Intel-SA-00271- 電圧変調に関するテクニカル・アドバイザリー
- Intel-SA-00280- BIOS 2019.2 IPU アドバイザリ
BMC/IPMI セキュリティ脆弱性アップデート 2019年9月3日
研究者たちは、Supermicro BMCの仮想メディア機能にいくつかのセキュリティ関連の問題を特定しました。これに対処するにはBMCファームウェアのアップデートが必要です。
CVE-2019-16649
CVE-2019-16650
AMDセキュリティ脆弱性: LinuxオペレーティングシステムにおけるSecure Encrypted Virtualization 無効なECC曲線点 (SEV ECC) の脆弱性
CVE-2019-9836
詳細を見るインテル四半期セキュリティリリース(QSR)アップデート2019.1、2019年5月
このアップデートは、インテル® Xeon® プロセッサーを搭載した X8、X9、X10、および X11 ファミリーの製品に適用されます。四半期ごとのセキュリティー・リリース (QSR) は、これまで個別に提供されていたセキュリティー・アップデートをまとめて提供するものです。
- インテル-SA-00213(CVE-2019-0089、CVE-2019-0090、CVE-2019-0086、CVE-2019-0091、CVE-2019-0092、CVE-2019-0093、CVE-2019-0094、CVE-2019-0096、CVE-2019-0097、CVE-2019-0098、CVE-2019-0099、CVE-2019-0153、CVE-2019-0170)
- INTEL-SA-00223BIOSは影響を受けません。
- INTEL-SA-00233(CVE-2018-12126、CVE-2018-12127、CVE-2018-12130、CVE-2019-11091)
これらの問題に対する BIOS アップデートは現在順次リリースされています。影響を受ける製品と必要な BIOS アップデートの詳細については、以下を参照してください。
インテル四半期セキュリティリリース(QSR)アップデート2018.4、2019年3月
このアップデートは、インテル® Xeon® プロセッサーを搭載した X11 ファミリー製品にのみ適用されます。四半期ごとのセキュリティー・リリース (QSR) は、これまで個別に提供されていたセキュリティー・アップデートをまとめて提供するものです。
- インテル-SA-00185(CVE-2018-12188、CVE-2018-12189、CVE-2018-12190、CVE-2018-12191、CVE-2018-12192、CVE-2018-12199、CVE-2018-12198、CVE-2018-12200、CVE-2018-12187、CVE-2018-12196、CVE-2018-12185、CVE-2018-12208)
- インテル-SA-00191(CVE-2018-12201、CVE-2018-12202、CVE-2018-12203、CVE-2018-12205、CVE-2018-12204)
"ネタバレ"インテル・プロセッサーの投機的実行に関する新しい研究論文
詳細を見るASPEED AST2400およびAST2500システム・オン・チップ(SoC)を使用したシステムに関するベースボード管理コントローラ(BMC)のセキュリティ脆弱性について
- CVE-2019-6260
スペクターとメルトダウンのサイドチャネル投機的実行
- インテル SA-00115(CVE-2018-3639, CVE-2018-3640)
- Intel-SA-00088(CVE-2017-5715、CVE-2017-5753、CVE-2017-5754)
- Intel-SA-00161(CVE-2018-3615、CVE-2018-3620、CVE-2018-3646)
インテル® マネージメント・エンジン (ME)、インテル® サーバー・プラットフォーム・サービス (SPS)、およびインテル® トラステッド・エグゼキューション・エンジン (TXE) に関するインテル® セキュリティの脆弱性について
- Intel-SA-00086(CVE-2017-5705、CVE-2017-5708、CVE-2017-5711、CVE-2017-5712、CVE-2017-5706、CVE-2017-5709、CVE-2017-5707、CVE-2017-571000)
BIOS/BMCファームウェア 2017年以前のセキュリティアップデート
2017年以前に公表された「一般的な脆弱性と暴露に対するファームウェアの修正」を参照してください。
Supermicro は、セキュリティコミュニティと積極的に協力し、当社の製品ライン全体のセキュリティを特定し強化しています。Supermicro ファームウェアで公開されている CVE の解決策をご確認ください。
詳細を見るセキュリティに関するよくある質問カテゴリー "セキュリティ "を選択
製品セキュリティ問題の報告
Supermicro製品でセキュリティ上の問題に遭遇した場合は、以下の詳細を添えてsecure@supermicro.comまでメールを送信してください。
- 製品名/SKU
- 脆弱性に関する詳細レポート
- 複製指示
- 関連するCVE
機密情報や秘匿性の高い情報を平文の電子メールに含めないでください。メッセージの暗号化にはPGPキーを使用してください。Supermicro製品セキュリティチームがお客様のレポートを確認し、問題の共同解決のためご連絡いたします。
詳細を見るSupermicroの製品セキュリティアップデートの最新情報を入手する
今すぐ購読する
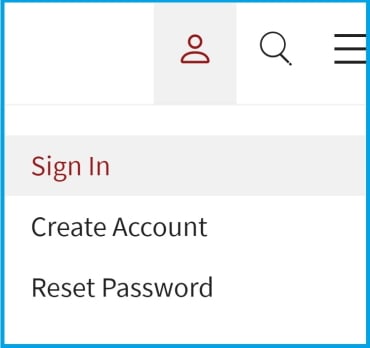
今後のSupermicroセキュリティアラートを受信するための購読を開始するには、以下の手順を実行してください:
1.画面の右上に移動し、サインインするか、シングルサインオン(SSO)アカウントを作成します:
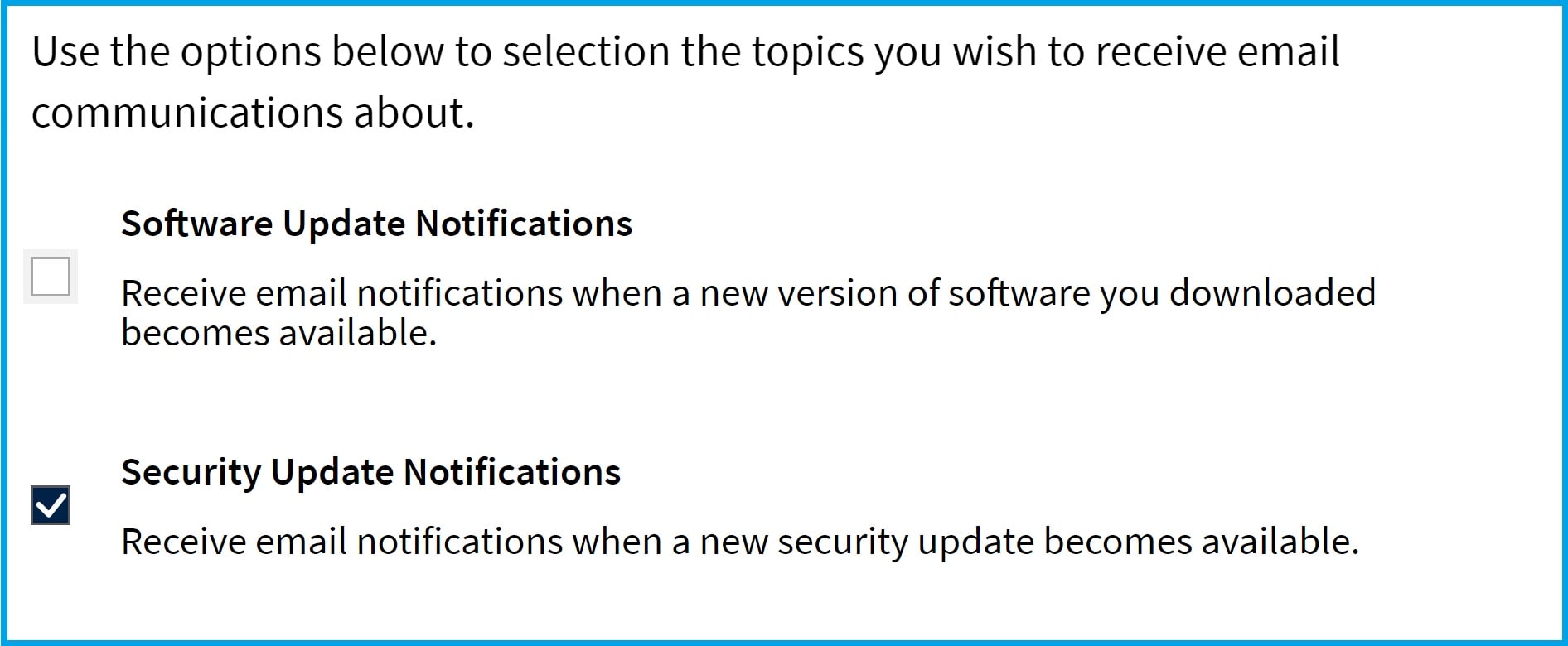
2.メール設定の管理」を選択します。

3.セキュリティ更新通知をチェック
- 発効日
- 最終更新日
概要
Supermicroでは、当社製品およびサービスのセキュリティと完全性の維持に尽力しています。この製品ライフサイクル終了(EOL)セキュリティポリシーは、EOLステータスに達した製品のセキュリティ問題への対処方法を概説し、透明性を確保し、お客様がアップグレードや移行を計画するのに役立ちます。
終末期(EOL)とは?
製品またはサービスは、開発、保守、強化が終了したことを公式に発表した時点で、EOLとみなされます。
セキュリティ・サポート・タイムライン
レガシー製品からの移行には時間がかかることを理解しています。お客様をサポートするために
- 深刻度が「クリティカル」(9.0~10.0)および「高」(7.0~8.9)のセキュリティ問題は、EOL発表日から3年間、引き続きサポートされます。
- この期間中、報告された脆弱性を評価し、重大性と影響に基づいてパッチや緩和策を発行することがあります。
- 3年経過後は、セキュリティの更新や調査は行われません。
例外
標準の3年間を超える延長セキュリティサポートは、別途契約により提供される場合があります。オプションについてご相談いただくには、Supermicroまでお問い合わせください。
お問い合わせ
このポリシーに関するご質問やご不明な点がございましたら、弊社のセキュリティチームまでお問い合わせください: secure@supermicro.com